Join Our Telegram Group
Thekeep3r (KP3R) platform, a significant player in the DeFi space, experienced a targeted attack that resulted in the loss of approximately 4,084 KP3R tokens, equivalent to around $200,000 USD.
Thekeep3r (KP3R) is a decentralized job marketplace within the DeFi ecosystem. It acts as a bridge between external projects and job providers, ensuring the efficient and reliable execution of tasks. KP3R plays a vital role in maintaining the stability and functionality of various DeFi platforms, including yield farming, lending, and other liquidity-related protocols.
The Attack: A Closer Look
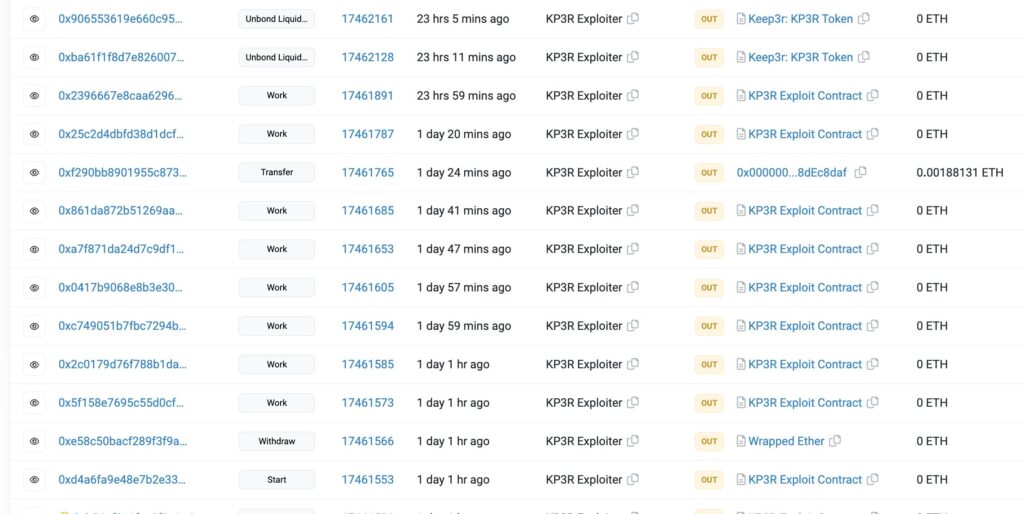
On the recent day, thekeep3r (KP3R) experienced a malicious attack that resulted in a significant loss of funds. The attacker managed to harvest approximately 4,084 KP3R tokens, which have an estimated value of $200,000 USD. The details surrounding the attack are still being investigated, but initial findings suggest that the attacker gained unauthorized access to the system through various means.
Exploiting a Privileged Vanity Address
One of the key vulnerabilities exploited by the attacker was a privileged vanity address, which granted them access to sensitive information. By compromising the governor’s private key, the attacker obtained the necessary permissions to modify the governor of several pools. This exploit allowed them to execute a reentrancy attack, further compromising the integrity of the affected contracts.
The Reentrancy Attack: Modifying the Governor of Pools
In the context of this attack, a reentrancy attack refers to a scenario where an attacker repeatedly calls a vulnerable contract before the previous invocation has completed. By exploiting this vulnerability, the attacker can manipulate the contract’s state and perform unauthorized actions. In the case of KP3R, the attacker modified the governor of multiple pools, thereby gaining control over crucial aspects of the platform’s operations.