Join Our Telegram Group
@BeosinAlert reported a stack overflow vulnerability was exploited in the $ARA token contract, resulting in a significant financial loss of $125,000. The attack was carried out by an identified 0xF84efA8a9F7E68855CF17EAaC9c2f97A9d131366. The root cause of the exploit was traced back to a bug in the contract’s handling of permissions.
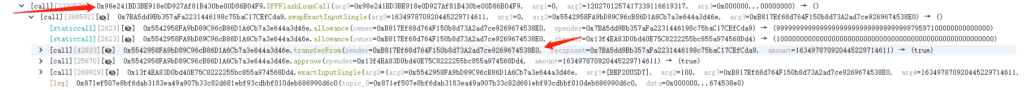
The attacker executed the exploit using the following steps:
1. Flashloan Acquisition:
The attacker initiated a flashloan for a substantial amount of 1,202,701 USDT (Tether) from a lending platform. Flashloans allow users to borrow a significant amount of cryptocurrency without collateral, as long as the borrowed amount is returned within the same transaction.
2. Swapping $ARA for USDT:
With the borrowed funds in hand, the attacker called a swap contract to convert 163,497 ARA tokens into 123,246 USDT.
3. Price Manipulation:
The flashloaned USDT was then used to purchase 504,469 ARA tokens, driving up the price of $ARA in the market. This step aimed to create an opportunity for the attacker to exploit the contract’s approval mechanism.
4. Additional Swapping and Unauthorized Transfer:
Taking advantage of the inflated $ARA price, the attacker made another swap, converting 132,123 USDT into 12,179 ARA tokens. The purpose was to allow an approved address to withdraw the funds from the swap contract.
Through these orchestrated actions, the attacker managed to exploit the vulnerability and illicitly transfer a substantial amount of funds.
